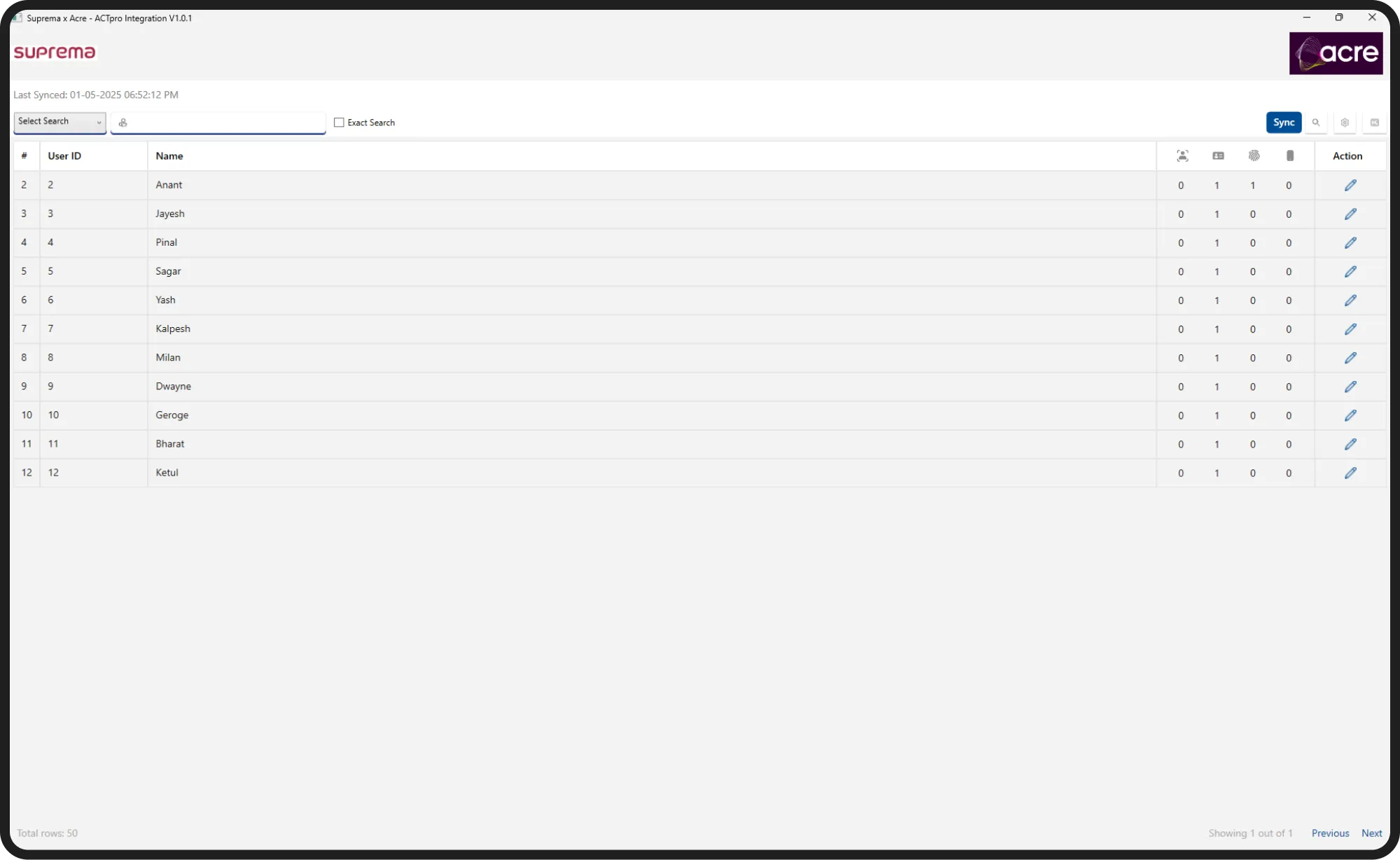
About Suprema x Actpro Connector
Synchronizing Biometric Systems with Access Control Systems
In the modern enterprise environment, organizations often use multiple systems for security and access management. While some systems offer cutting-edge biometric devices, others have robust access control modules. The Suprema x Actpro Connector acts as an intelligent middleware that synchronizes user operations automatically between such disparate systems, ensuring security operations remain efficient, accurate, and scalable.

Project Challenges
Developing the Suprema x Actpro Connector involved overcoming critical challenges:



System Interoperability: Integrating two entirely different systems — one focused on biometrics (Suprema) and another specialized in access control (Actpro) — without altering their core structures.



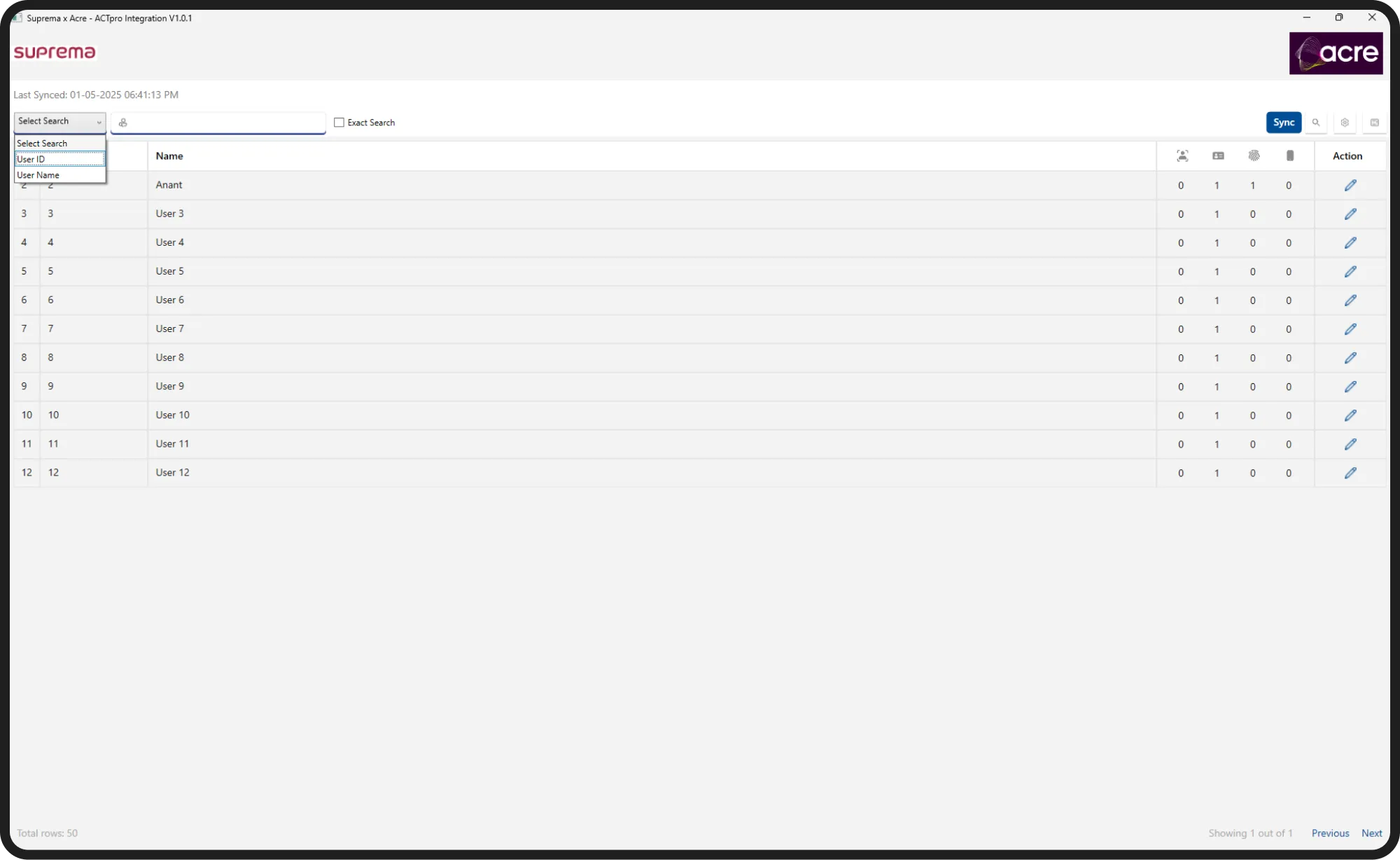
Manual Sync Elimination: Previously, super admins had to manually add, update, or remove users across systems, leading to delays and high error rates. Automating this sync was essential.



Real-Time Biometric Integration: Ensuring that fingerprint and face data, once registered in one system, immediately and reliably syncs to the other system for instant access authorization.



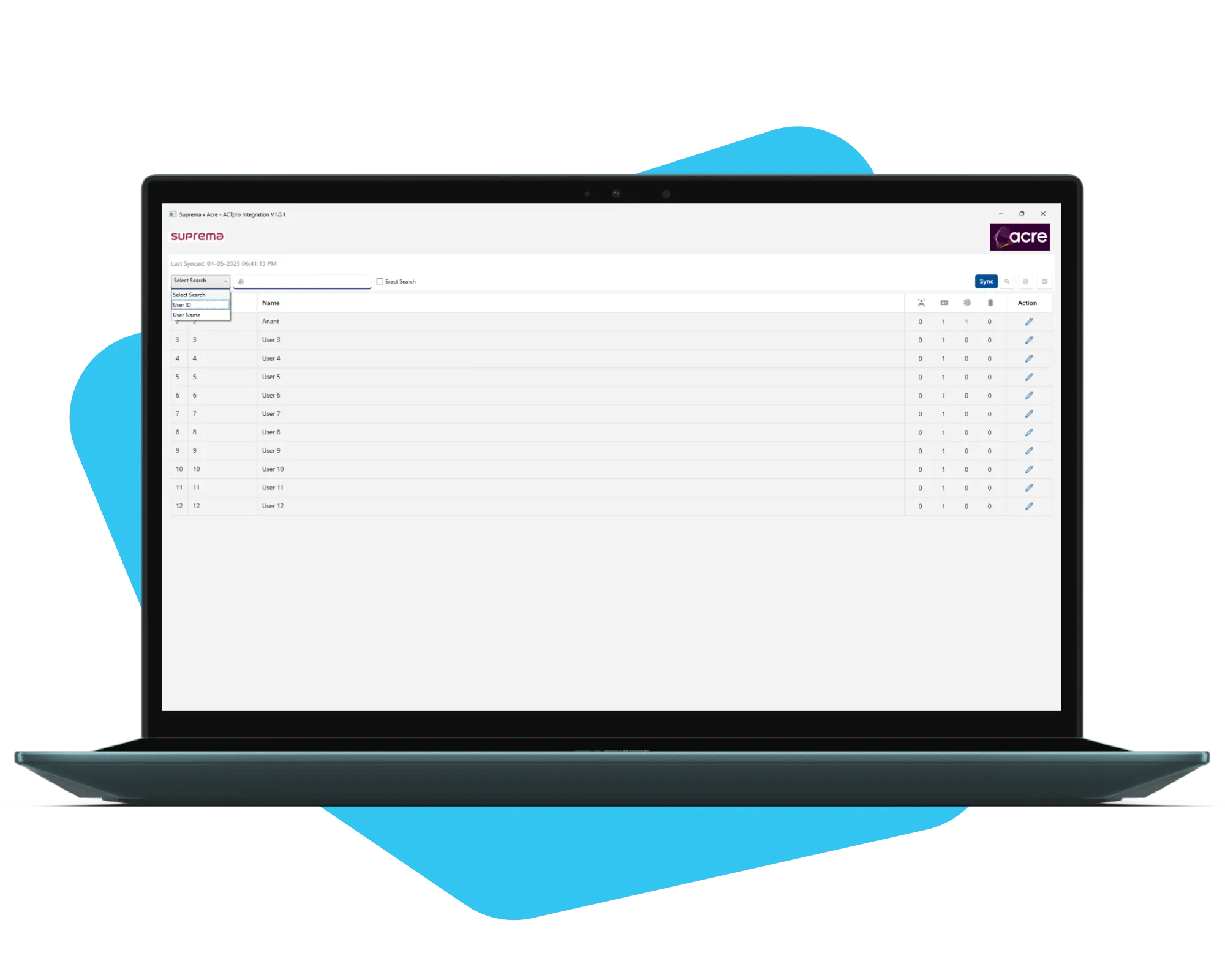
Device Management and Access Logs: Creating a seamless interface for admins to manage entry/exit devices and verify access logs in real-time for all user activities.
How Did We Help?
Creole Studios approached the development of the Suprema x Actpro Middleware with a structured and targeted strategy:
Detailed Technical Discovery
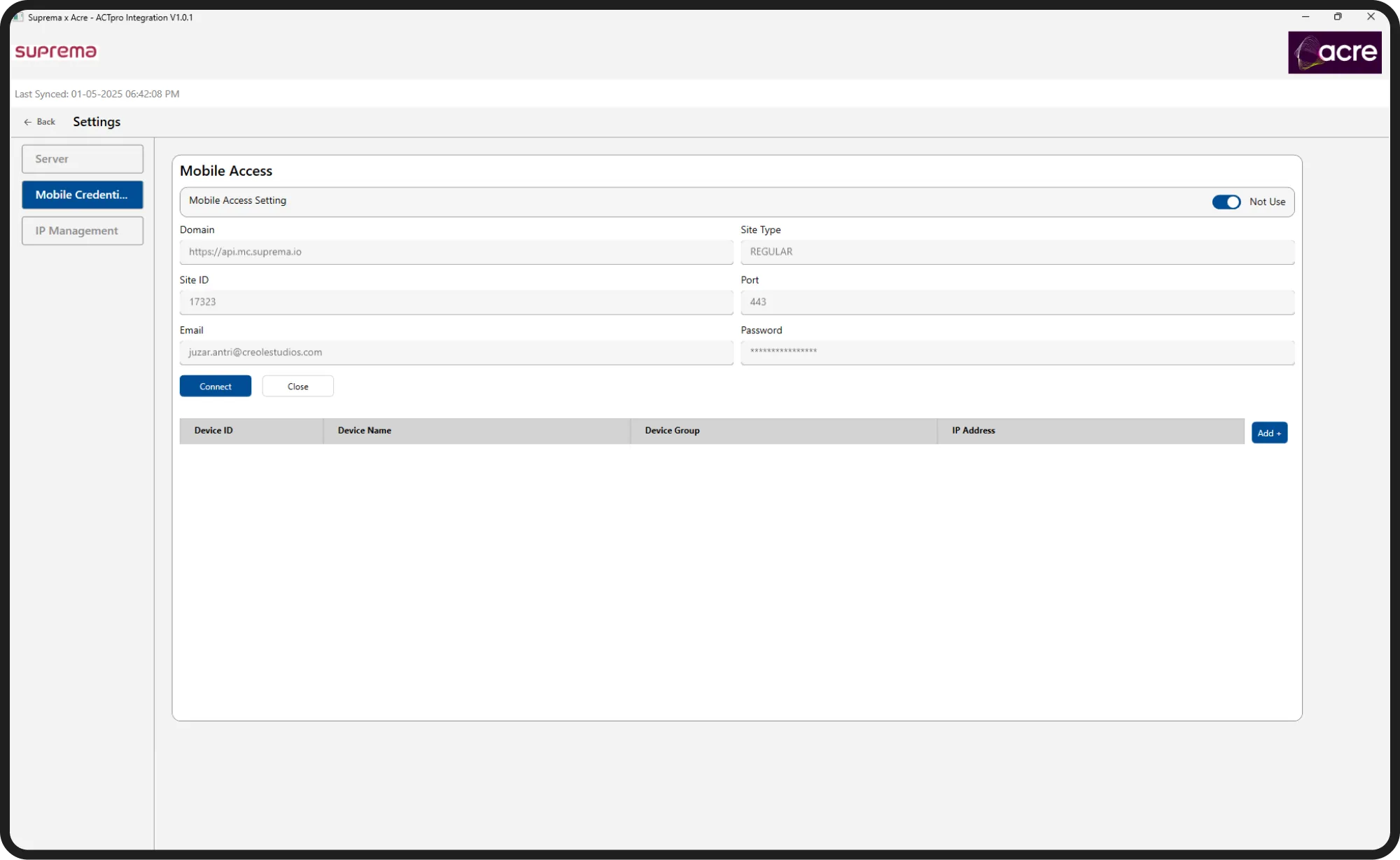
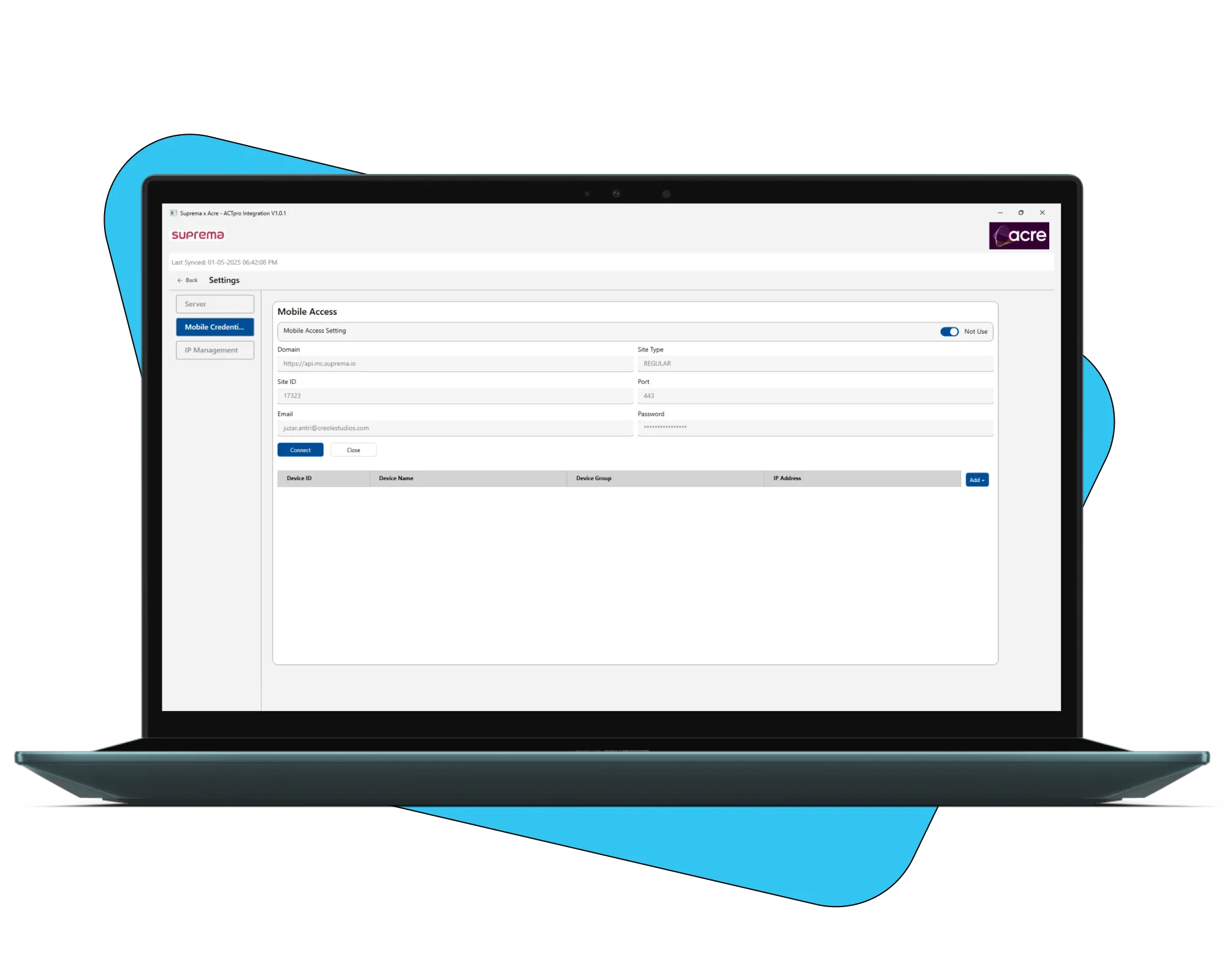
We conducted technical discovery sessions to deeply understand the APIs, data flows, and communication protocols of both Suprema and Actpro systems. This phase ensured that we mapped user data and operational triggers accurately across both platforms.
Middleware Architecture and Design
We designed a middleware that acted like a smart translator, capable of understanding, converting, and syncing operations between the two systems without data loss or latency.
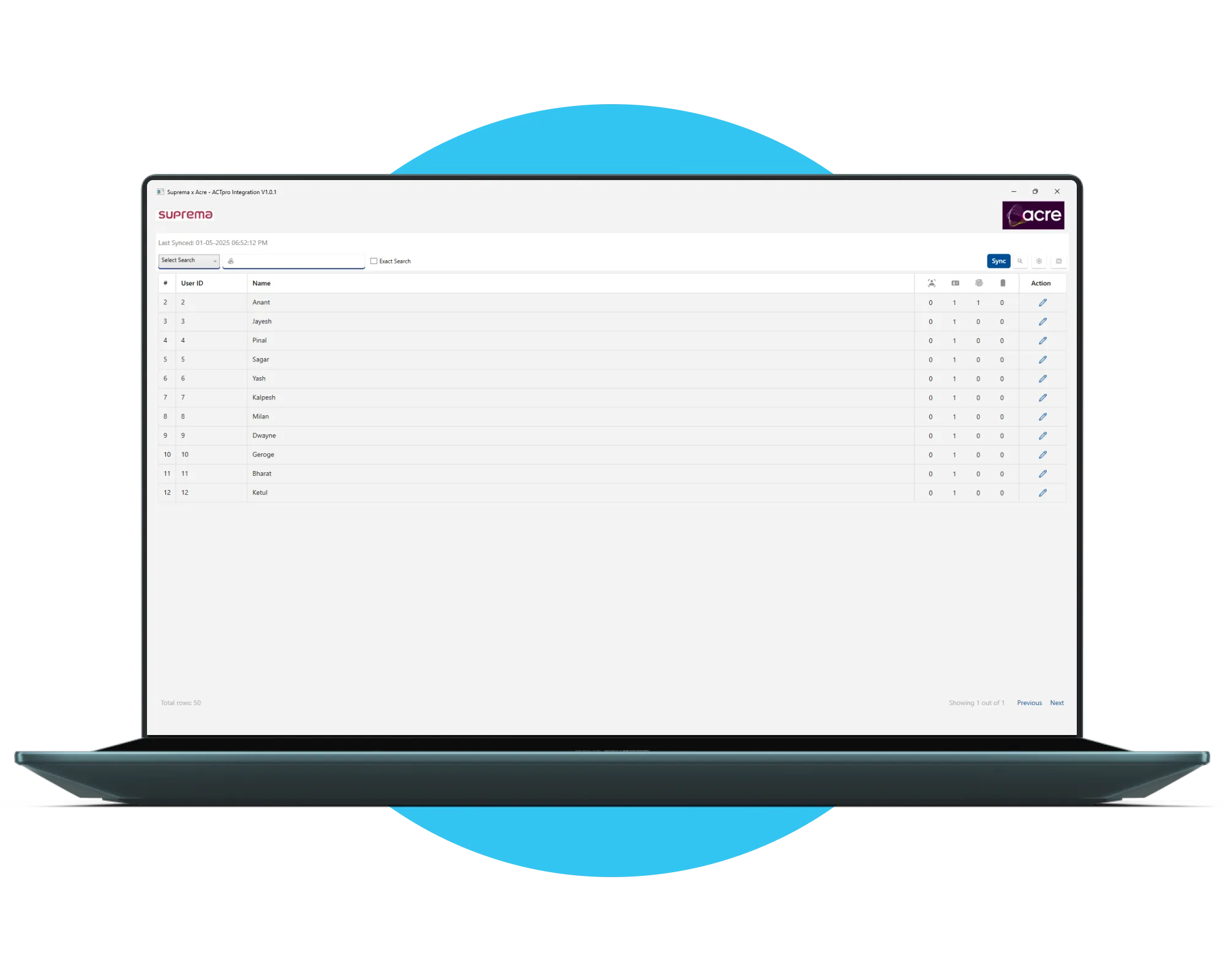
Real-Time Sync Development
Whenever a user is added, updated, or deleted in one system:
- The middleware captures the event instantly.
- It processes the information.
- It triggers corresponding operations in the second system without manual intervention.
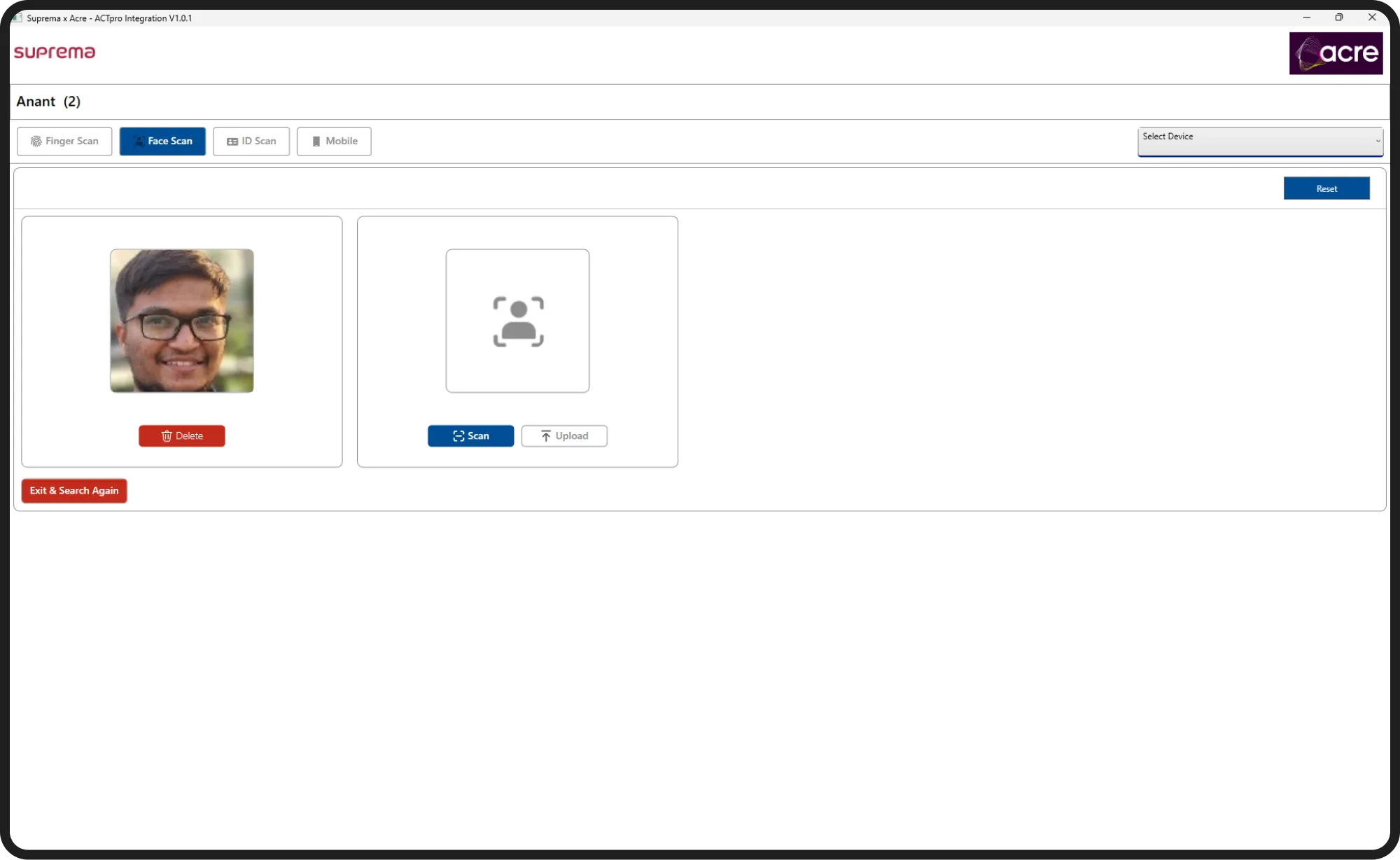
Special focus was given to syncing biometric data (fingerprints, facial IDs) for access grant operations.
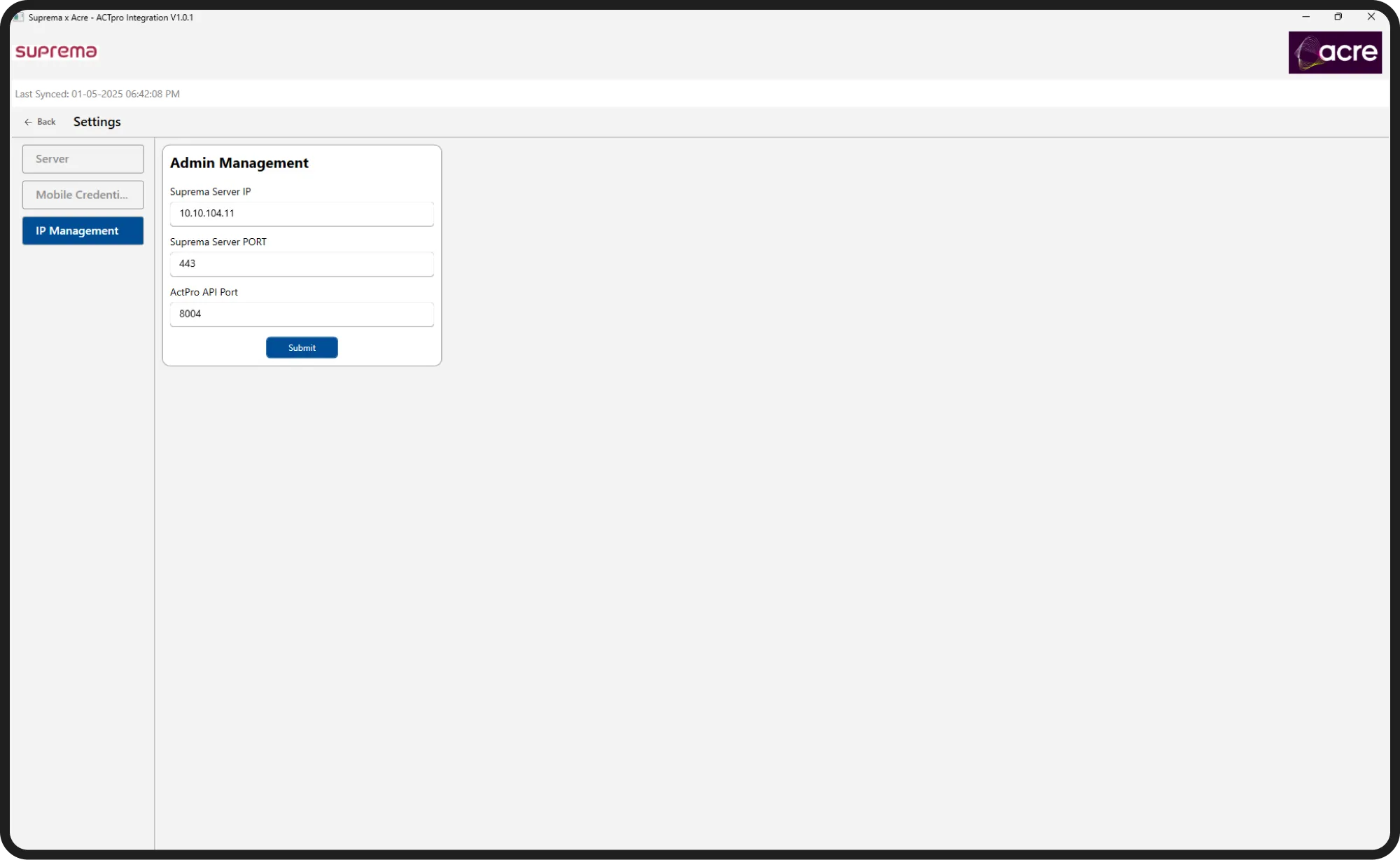
Device and Access Control Management
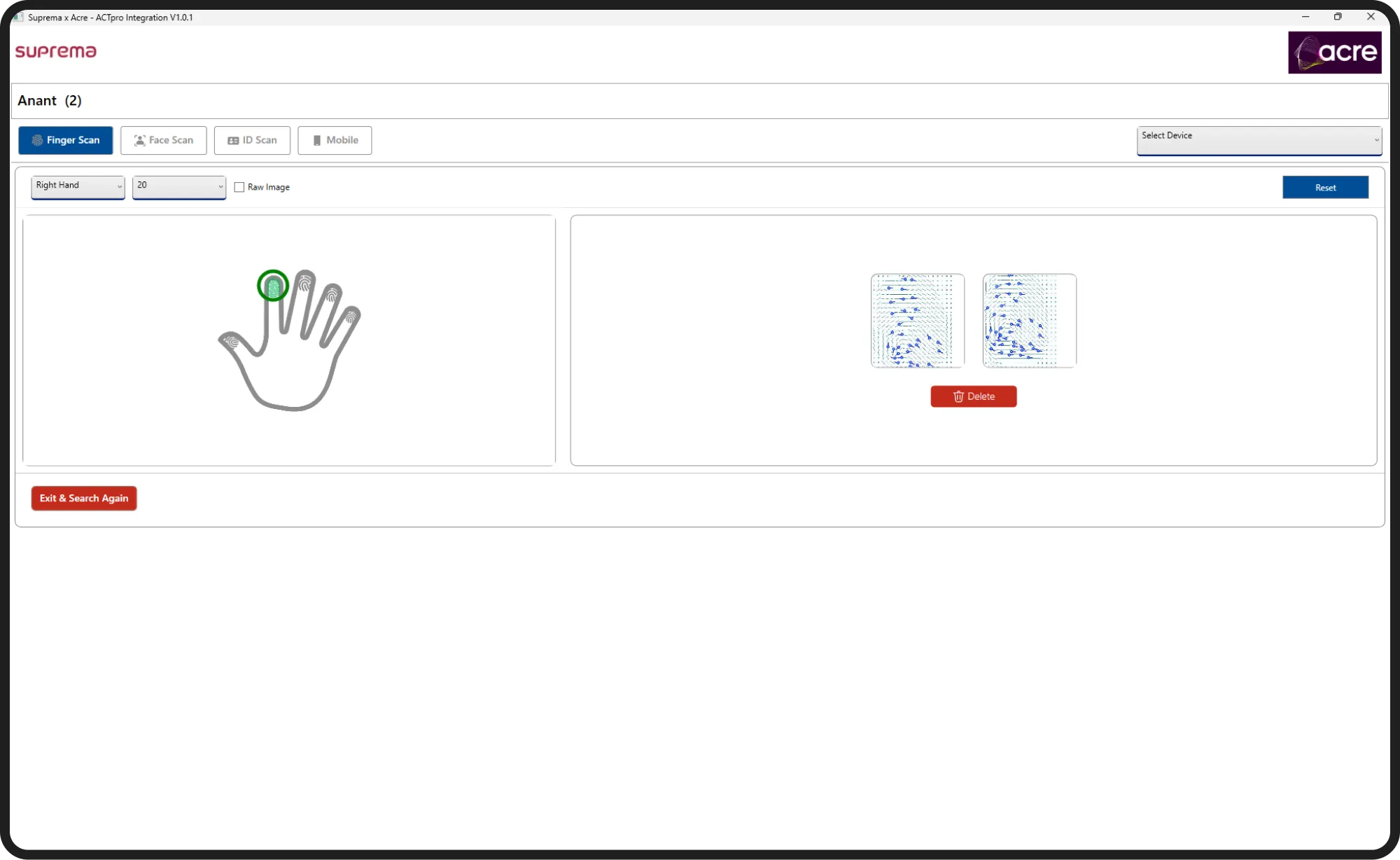
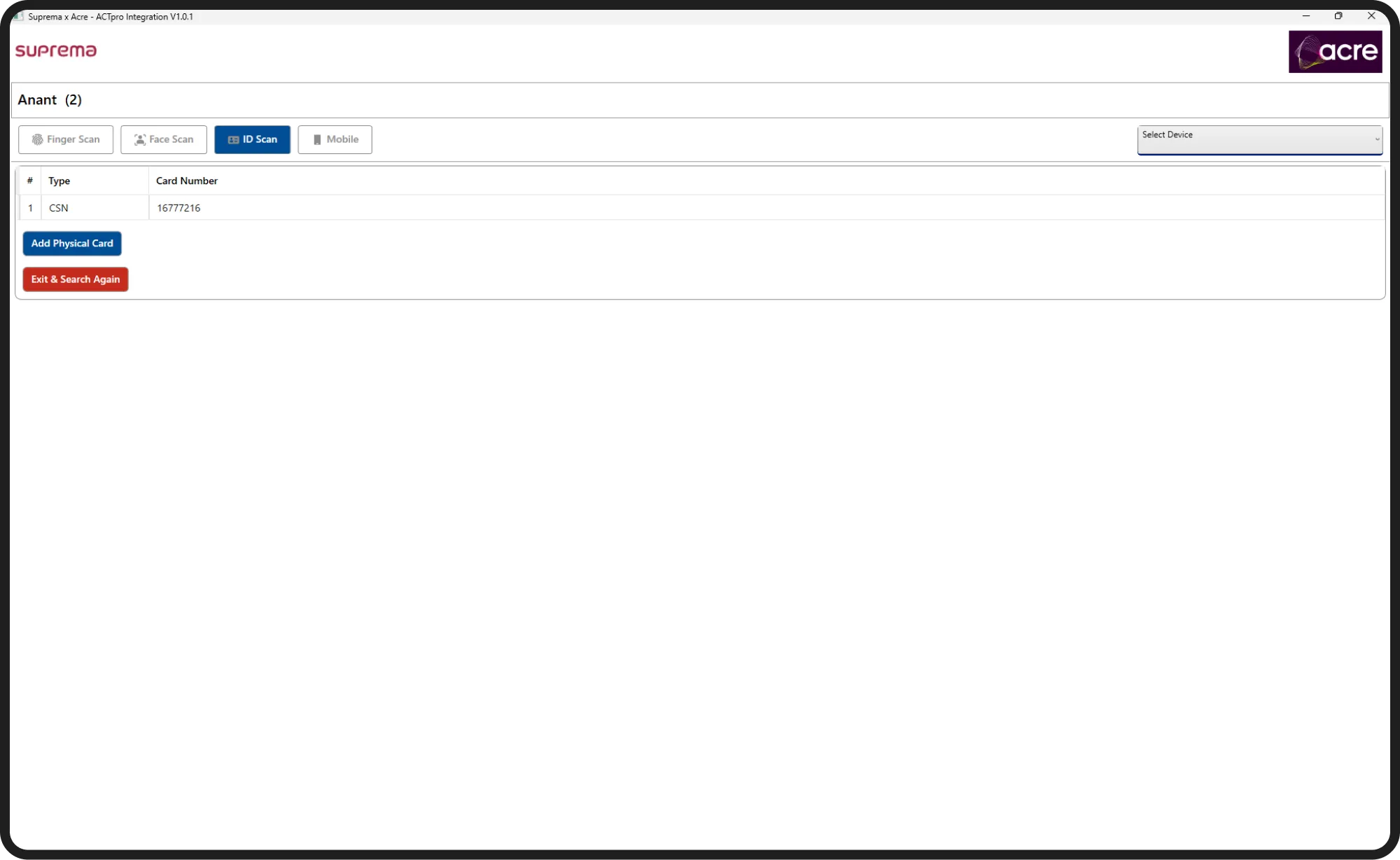
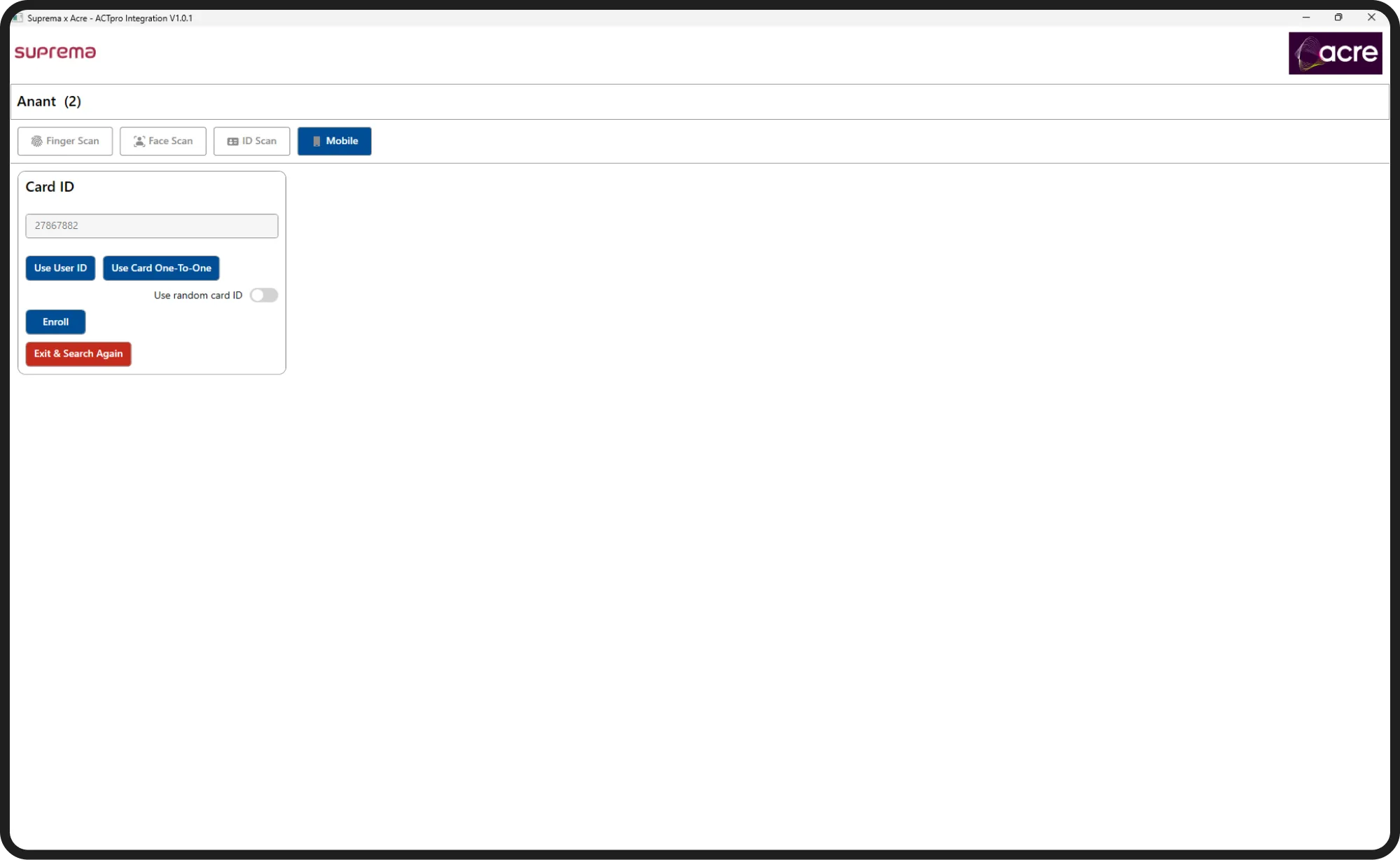
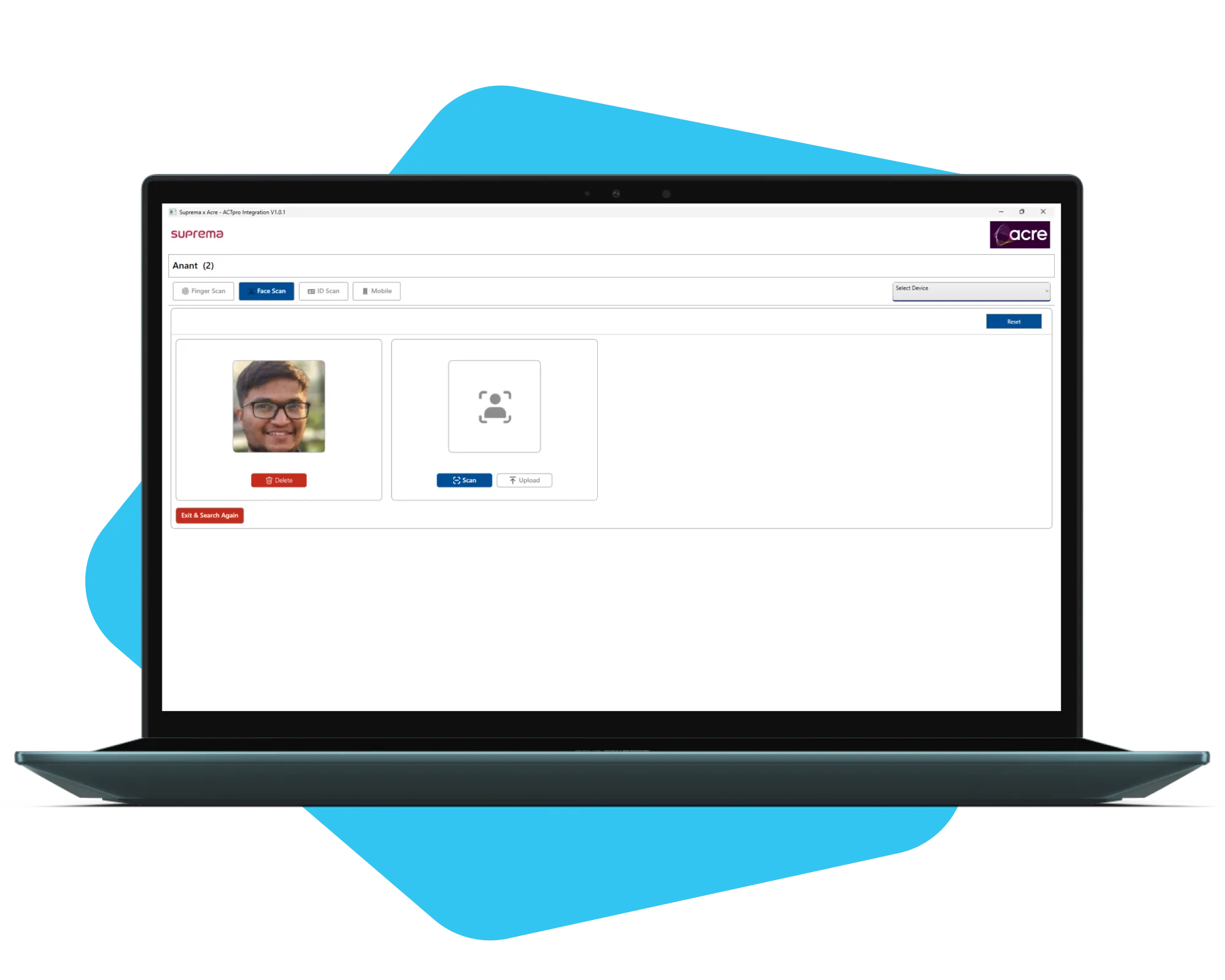
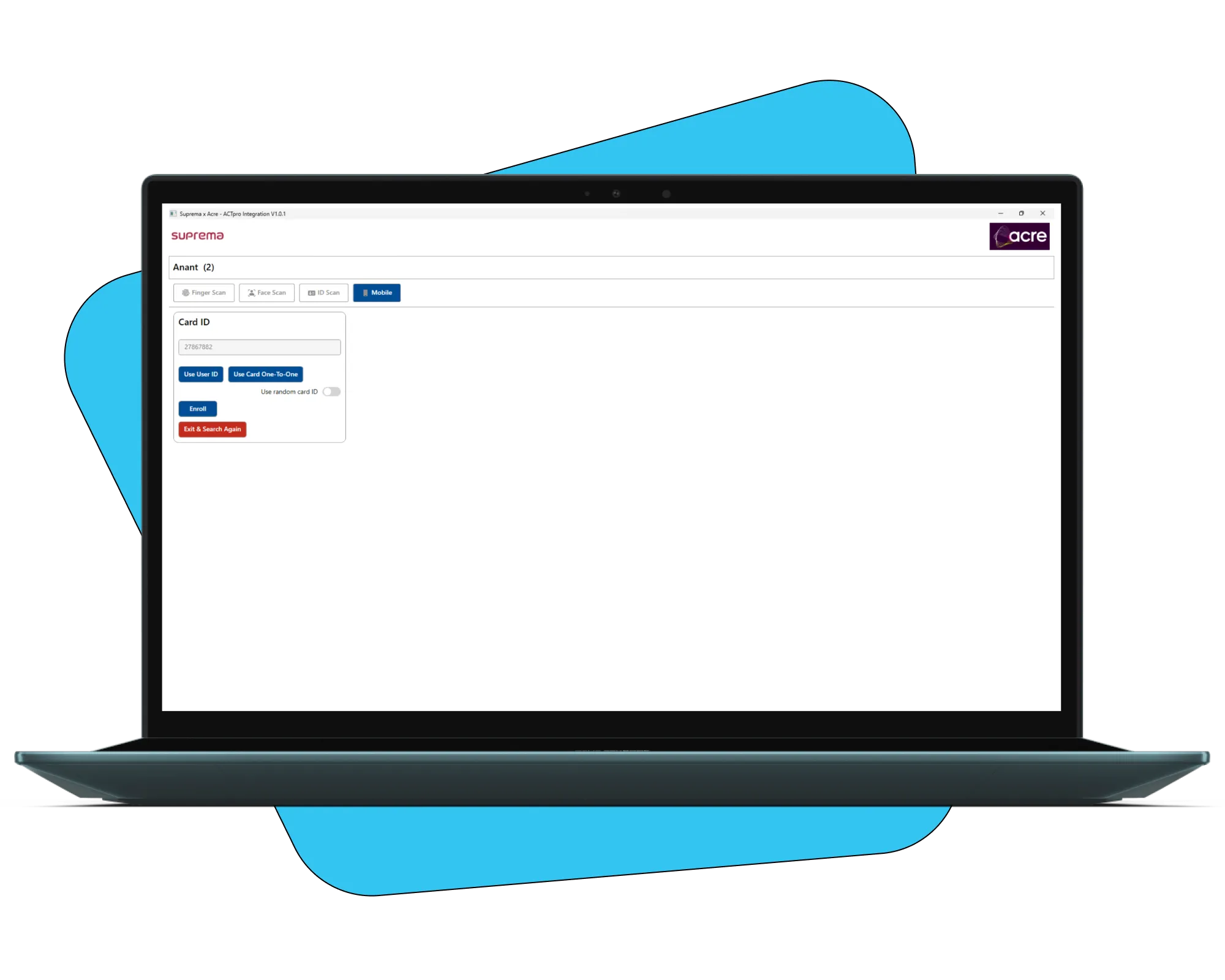
We built interfaces for:
- Assigning fingerprints and facial IDs to devices.
- Managing entry and exit devices.
- Verifying access logs for security teams to track real-time user movements.

Testing with Real Devices
Rigorous field testing was conducted:
- Scanning fingerprints and facial data on entry/exit devices.
- Verifying that access was granted instantly on both systems.
- Simulating high-volume operations to ensure performance stability.
Team Structure and Management
Our delivery team included:
- 2 Backend Developers
- 1 Hardware Integration Specialist
- 1 QA Tester
- 1 Project Manager
We ensured seamless collaboration between software and hardware teams during integration and testing phases.
The Outcome
The Suprema x Actpro Connector transformed how companies manage security operations across multiple systems.
Key outcomes include:
- 100% elimination of manual syncing between biometric and access control systems.
- Instant access provisioning after user registration.
- Reduced security risks by ensuring all employees had appropriate access at all times.
- Operational efficiency with reduced workload for IT and security staff.
This solution empowered enterprises to scale their operations without worrying about syncing gaps or human errors.